I wanted to highlight a recent project I help a client out with, where we used CFConfig to help automate the process of applying government STIGs to ColdFusion servers. A STIG, or Security Technical Implementation Guide, is meant to standardize the process of setting up and auditing secure servers. If you manage servers in a government or corporate setting, you may be familiar with this. If not, you should still be automating your locks downs anyway, so keep reading.
So first things first, CFConfig is primarily a CLI tool that runs on CommandBox, however this article is NOT about CommandBox servers. In fact, the client in question doesn't use CommandBox at all, but just regular ColdFusion installations. They run CFConfig via a CommandBox installation on a thumb drive so it's never even installed and nothing remains on the server. Of course, if you're using CommandBox for your servers, it gets even easier, but this is not a requirement. And finally, credit goes to George Murphy for coming up with this idea and helping assemble all the required lock down elements.
STIG
So back to the STIG, here's an example lockdown guide for ColdFusion
https://www.stigviewer.com/stig/adobe_coldfusion_11/
Among other things, they cover dozens of settings that must be checked in the ColdFusion administrator-- a process which is manual, time consuming, and prone to mistakes. We reviewed the lockdown requirements for our project and enhanced CFConfig to ensure it supported all of the settings that we needed to automate. Then, we created a JSON file representing the lockdown profile that was required for the application servers. Note, if you're already using CFConfig to manage your datasources, custom tags, or mappings, your lockdown settings can be incorporated into that same JSON, or into a separate JSON you apply only on top of production servers.
So given the file above which is an EXAMPLE, you can apply it to any ColdFusion server like so:
box cfconfig import STIG-CFConfig.json C:/coldfusion2018/cfusion
Adjust the filename and server home path as necessary. You can review the docs for this here:
https://cfconfig.ortusbooks.com/using-the-cli/command-overview/import-settings
And just like that you can apply hundreds of individual lock down settings to a server in seconds.
Reporting
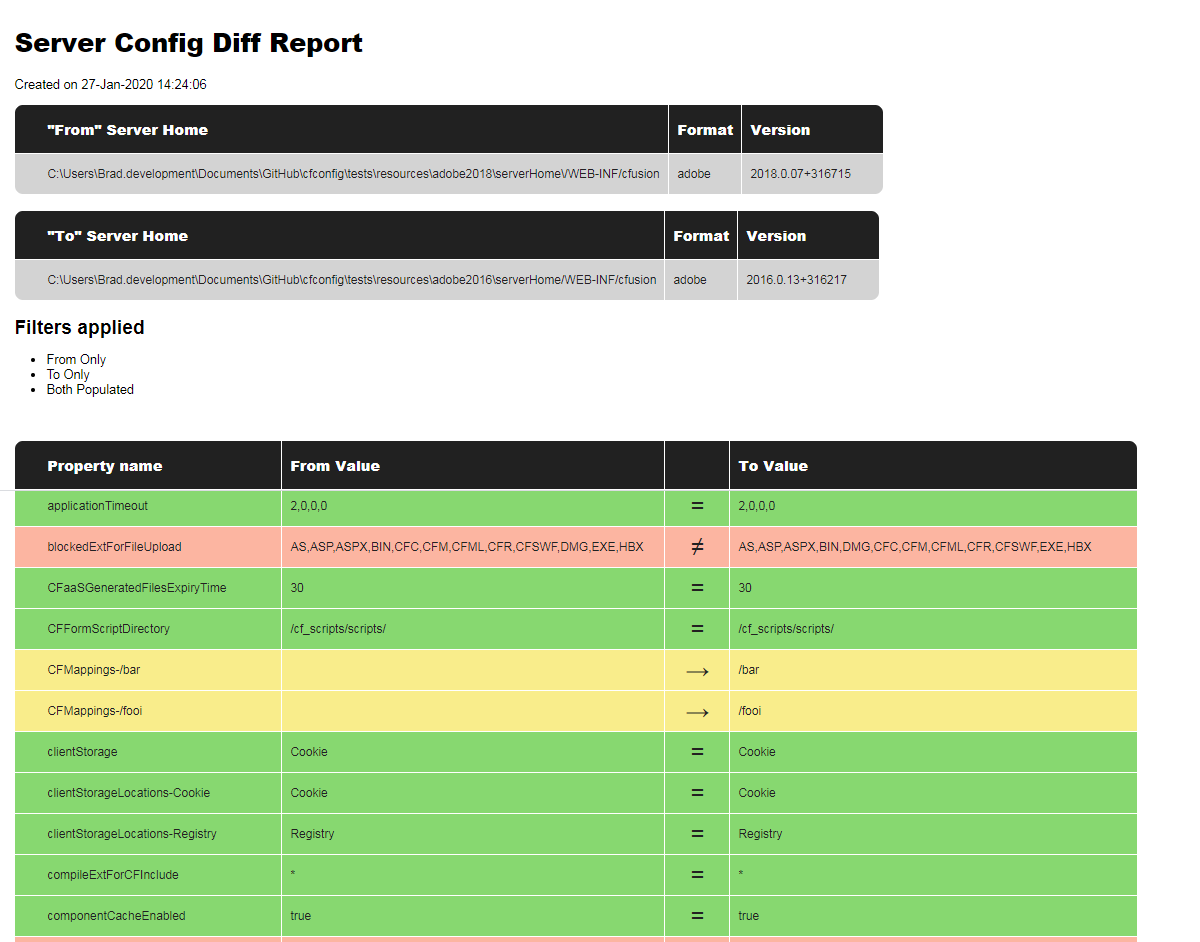
The other nifty thing that George used CFConfig for was nightly reporting to verify if anyone had changed any settings directly in the administrator of the servers. Again, this was done by running CommandBox out of a temporary folder on the machines so nothing was ever "installed", which made it much easier to get approval for the process. CFConfig has a cfconfig diff command that can compare two servers OR a server and a config JSON file and report any differences between the two. We added the ability to export the diff report to HTML or PDF so you can create an audit trail of whether your server's settings match the "gold standard" you define in a JSON file.
box cfconfig diff gold-standard.json C:/ColdFusion2018/cfusion/ PDFReportPath=C:/nightlyDiffReports/
And you get a report that looks like this:
Conclusion
Hopefully this gives you some ideas on how to automate the lockdown of your server configuration. The links and JSON file above were used with ColdFusion, but everything here applies to Lucee as well. Also keep in mind, the JSON file I provided is an example. Please modify it to suit your needs.
And one final note, Adobe ColdFusion 2016+ will overwrite config on disk with the config stored in memory. That means you must stop the server before applying any configuration changes via CFConfig and the restart the server to pick them up.



Add Your Comment